How do I make my application more secure? Where do I get security requirements from? Why do I need security requirements?
If you have an application, these are some of the questions you may have.
What are security requirements?
Security requirements describe what is expected of a system and how it should function. Security requirements define what assurance criteria should be built into the system to provide the right level of protection for the kinds of data and functionality the system provides.
Where do you find security requirements?
Where do you find security requirements, how do you get them, and where do they come from?
OWASP has a document called the Application Security Verification Standard (ASVS) that provides close to 300 controls related to security.
Are all of them appropriate for you? Perhaps not, and that’s why ASVS groups these controls into 3 categories or into 3 levels of assurance:
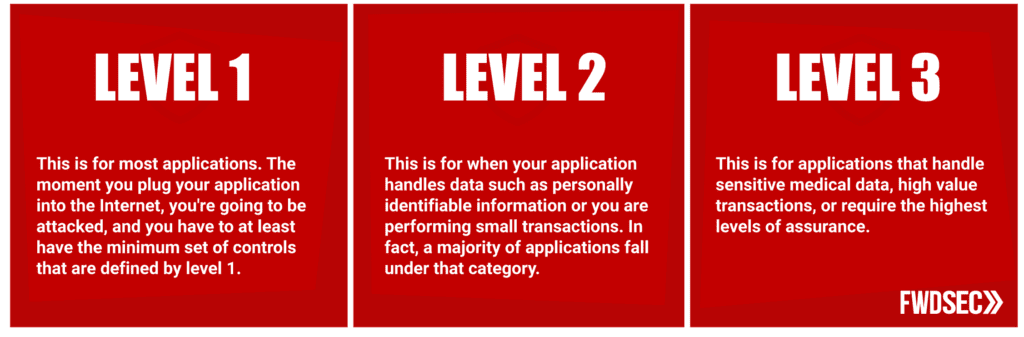
Level 1 is for most applications. The moment you plug your application into the Internet, you’re going to be attacked, and you must at least have the minimum set of controls that are defined by level 1.
Level 2 is for when your application handles data such as personally identifiable information or performing small transactions. In fact, most applications fall under this category.
Level 3 is for applications that handle sensitive medical data, high value transactions, or require the highest levels of assurance.
At Forward Security, we use ASVS every day to perform our testing and you should also use it to build secure applications.
How Mature is Your DevSecOps?
Our comprehensive DevSecOps Maturity Assessment covers 8 key phases of DevSecOps practices, 29 questions in total.
By evaluating your team on each capability, you can determine if your DevSecOps maturity level is early, intermediate, or advanced. Your assessment includes a custom report that provides your overall maturity as well as detailed recommendations you can take to enhance your security posture.