There are several big problems with automated security scanning tools.
In this post, we’ll discuss some of the major problems with the tools and what you can do to overcome them.
Too Many False Positives
Perhaps the biggest challenge with automated security scanning tools is that they produce too many false positives, which is when the scanners detect so many issues (most no – low risk) that it becomes overwhelming and time consuming to deal with. This causes developers to suffer from false-positive fatigue and major issues go unnoticed. The tools don’t know the business, so they have no way of prioritizing the issues in term of risk. Tools can produce generic severity ratings, but without taking the unique business into account, those ratings are meaningless.
Continue reading: The Importance of Using a Risk-Based Approach
If the tool produces too many false positives, many developers end up turning them off and stop using them altogether. This not only becomes costly, but the organization is also not getting the value from the tool and major issues are not being addressed.
In some cases, we’ve seen companies buy licenses to a tool, but get stuck on the installation stage so they don’t even use it.
Believe it or not, but this scenario is quite common.
Too Much Reliance on Automation
There’s a saying in security – ‘tools don’t solve problems; people do.’
Many pentesters rely on these automated tools, but they are too limited. There also isn’t a standard definition of a pentest, so any automated scan could be considered a pentest. However, automated scanners don’t catch everything. For instance, the tool cannot determine whether a certain person within an organization has the necessary access control. To answer that, you need to understand the business and what access control each person ought to have, and then manually check it to ensure the permissions are assigned appropriately. This cannot be done automatically. To do security testing the right way, you need to do manual testing as well.
If you don’t have the right consulting support to make the tools successful, they are going to fail. The investment on whatever fancy tool you bought, is not going to work.
This is where professional services come in.
Unauthenticated Scans
Another big problem is that many tools on the market will scan your application, but they are not authenticated scans, or if they are, they are complicated to set up.
What is an authenticated scan?
Imagine someone who is looking to break into your apartment. As with most industrialized buildings, there are a few security measures in place. There’s a front door lock, security cameras, perhaps a concierge. Then there’s the elevator, which requires a key fob to activate. On each unit there’s at least one lock – sometimes a security system, perhaps a dog, etc.
Unauthenticated scans are akin to looking at the lobby from the outside and trying to understand the full scope of all the security measures in place. From this perspective, the burglar doesn’t have the necessary visibility to make any sort of meaningful assessment.
Many companies are buying tools that are doing unauthenticated scans, which don’t provide much value.
Often, we encounter companies that don’t have the right professional services SME support so they are not getting the most value out of their tools. We can make the tools work. So if you’re company bought a tool and haven’t set it up with authenticated scans, we have the expertise to set it up for you so you can do proper authenticated scans. We can enable it to dig a bit deeper, profile the tool, make it work better. We can make that tools work for their money.
Too Many Reports
Another activity where a lot of issues are discovered is through manual pentests. Whenever a skilled person is doing a manual review, they are bound to find issues, and those issues are typically logged in a spreadsheet, which is a fourth data source. So now you have reports from SAST, DAST, and SCA scanners as well as manual reports.
One scanner may find one issue, another finds another issue, and a manual test finds a third issue. On their own, each of these issues may not be that significant, but when combined, they could create an attack pathway that may be much more serious. Highlighting this attack scenario tells you where you should put your focus.
If you’re not correlating, you’re not honing your focus.
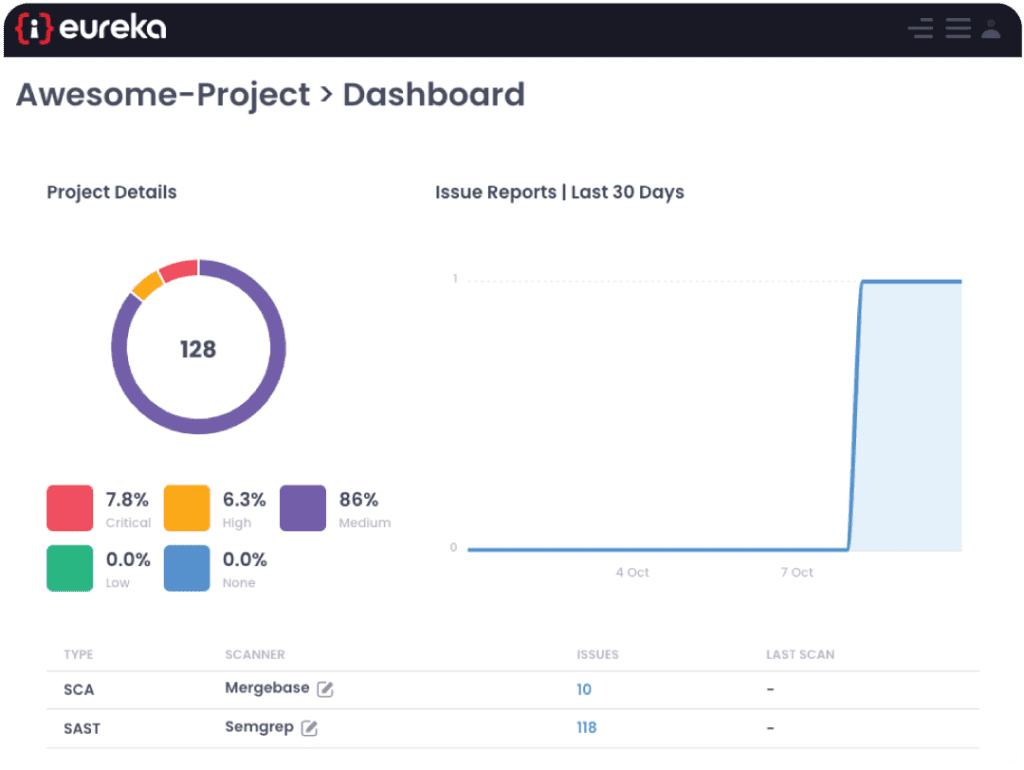
The Challenge with Multiple Scanners
For many larger organizations, it’s quite common to have multiple scanners. But this creates many challenges, namely:
- No standard location
- No global configuration
- Lack of central logging
- Multiple reports in different places
- Installation maintenance and patching for each of the scanners
If you’re not correlating the results from each of these scanners, then you’re not getting the value of the scanners. Issues will be overlooked, and developers will spend a lot of time reviewing false positives.
Eureka DevSecOps Solution
Our Eureka DevSecOps Service and Eureka DevSecOps Platform are designed to enable your team to get the most value out of your tools.
If you have automation tools:
- Tools won’t solve your problem, you need professional services to help you
- You likely need help installing and getting the tools set up
- You are not getting the most value from your investment
With our Eureka DevSecOps Service and Eureka DevSecOps Platform, we help organizations combine all their tools into one centralized platform so that you only have one global, normalized report. Eureka centrally correlates and aggregates issues from both manual and automated activities, reducing the number of false positives (thereby reducing false-positive fatigue), finding threat scenarios that may otherwise go unnoticed, reduce the number of scanners you need to install and manage, and have them all run from one place and under one agent.
Now your manual and automated scans are a lot more powerful, and your developers are no longer becoming bogged down with an overwhelming number of false positives. This is how you can get the most value out of your scanners and address major issues sooner.
Security Training
We offer security training and security subject matter expertise to your DevOps team so that your developers can be more security aware. We can also do DevSecOps teams, roll out AppSec programs, provide, assist with integration of CI/CD tools, conduct risk assessments, and so on.
If you are looking to strengthen your security posture, book your free consultation today.